Deny Local Log On for Azure AD accounts
Windows can be setup in shared PC or Kiosk mode. I have already written a blogpost about this. The aim is to provide a Windows experience for multiple users on one device, where the user may not even has his own (AAD) account.
Now on these devices you may want to restrict the ability to log in with certain accounts. If the device should be fully restricted for any domain/Azure AD accounts, you can follow this guide. This may be considered as a workaround, but I did not find a better solution to achieve it. It includes to create:
- Azure AD group — that holds members which should be restricted from sign-in
- Intune endpoint security profile — to add our group to the local guests group
- Intune configuration policy — to set the “Deny Log On” setting for a specific security identifier (SID), in our case the guest users
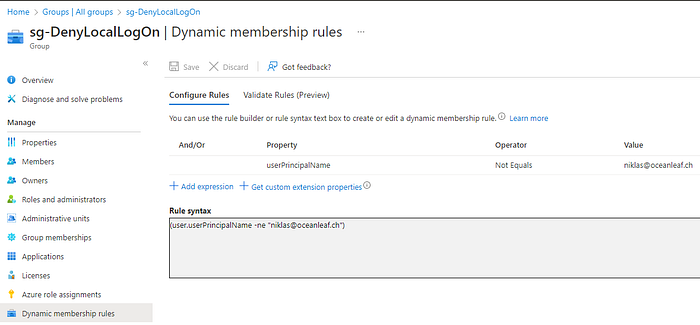
Step 1: Azure AD group
Just create a normal Azure AD group, this may be assigned or dynamic. If you want to block all Azure AD users from signing in, define the rule for example: include all users except your backup user.
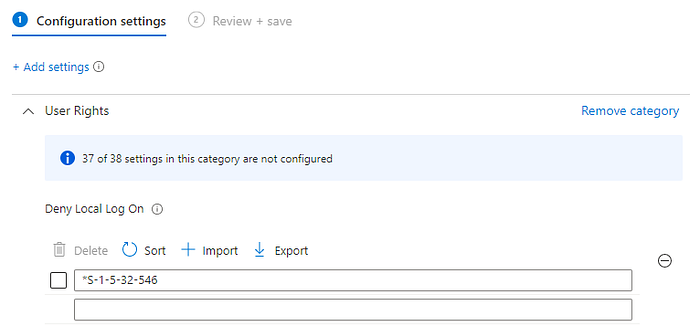
Step 2: Intune configuration policy
The configuration is a settings catalog item “Deny Local Log On”, here we insert: *S-1–5–32–546 this is a well known SID which stands for the guest users. (see more)
Step 3: Intune endpoint security profile
Last we will add our group to the local guests group with an endpoint security>account protection>Local user group membership profile.

For the end user this will be the result, when trying to sign in:

Notes
- It may also make sense to leverage another local group instead of the guest users
- From my experience it is not possible to add Azure AD group SID to the Deny Local Log On settings, maybe because this group is unknown (Azure AD Object ID to SID Converter)
- Shared PC Guest accounts will not be prevented from sign-ins, even if you block the guest users SID
