Intune EPM — enable for all app types!
Introduction
Microsoft’s Intune Endpoint Privilege Management (EPM) allows to run applications on Windows with elevated privileges, without the need to be local administrator.
The issue
> ⚠️ Update June 2024: EPM now supports .msi and .ps1 files!
EPM only supports ‘.exe’ files as of now as stated in the official documentation. This is quite a limitation, since many apps and software are of other file types.
The solution in short 💡
As a solution, I tested out if I could build a bat file that just calls another app and convert that to an executable. With EPM I would specify the file hash of my conjured file, so that any manipulation would result in a failure with EPM and there is no chance of exposing it. The solution indeed worked for me, and I thought it is worth sharing.
⚠️ This is an experimental solution. It may not be technically perfect, but only a workaround — use on your own responsibility.
Setup ⚒️
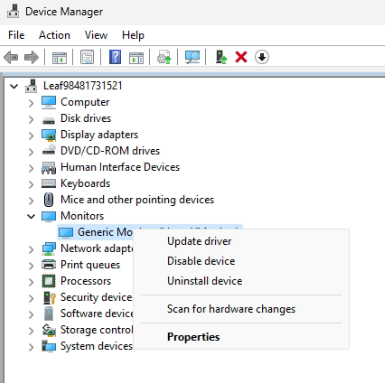
For my case, I want to make Windows Device Manager (which is devmgmt.msc) compatible with EPM.
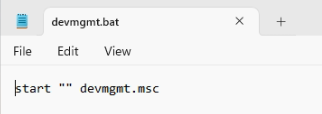
Bat file
To start, we create a .bat file with the following content, that starts devmgmt.msc and doesn’t output the cmd/bat:
Convert to executable
Next step is to convert our bat file to an exe. For that I make use of IExpress Wizard, which is natively installed on Windows.
Run it as admin and follow these steps:


The result is an executable file:

From that we need the file hash, to create the EPM policy afterwards. Make sure you already have an EPM settings policy applied in order to use these PowerShell code snippets. First, import the module of EPM tools:
Import-Module 'C:\Program Files\Microsoft EPM Agent\EpmTools\EpmCmdlets.dll'Then, get the file attributes (replace your file path + name):
Get-FileAttributes -FilePath "<insert path to just created executable>"It should look like this:
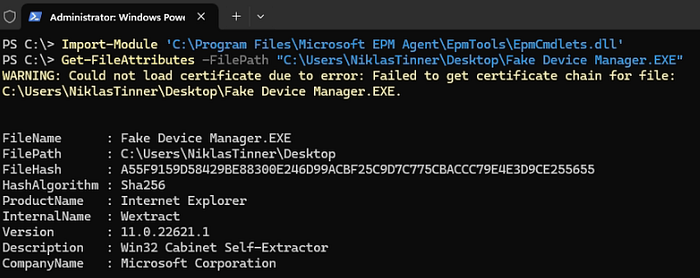
Copy the FileHash value from here.
EPM rules policy
To create the policy and make our file eligible for EPM, navigate to the Intune portal > Endpoint Security > Endpoint Privilege Management
❗ Make sure you already have an EPM settings policy deployed at this time.
Create a new elevation rules policy:

Name it and configure the first instance.
- Add a rule name (freetext)
- Add elevation conditions, if needed
- Set the child process behavior to “Allow all chiled processes to run elevated”
- Insert the file hash value
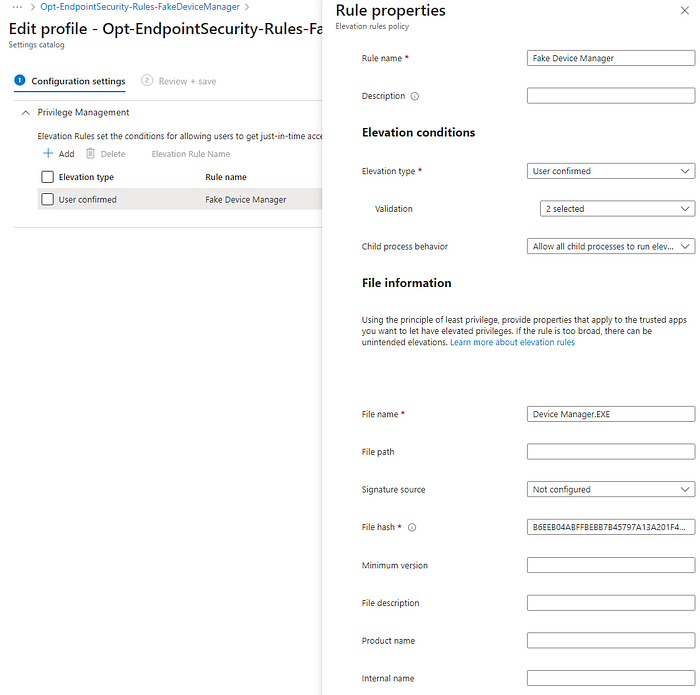
Assign the policy and wait until it was applied.
Demo 🔴
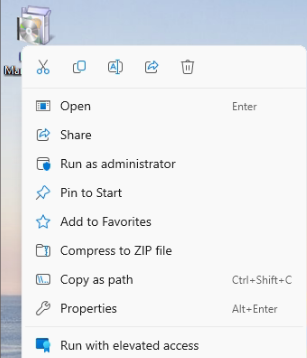
Now try to run the executable with elevated access.
Fulfill the validation (if configured). The Device Manager should now be started with admin permissions for a standard user 🎉:
Bonus: Package for Intune 📦
If you want to deploy your fake executable app with Intune, follow these steps:
Prepare an empty folder with 2files: your fake executable and an install.ps1 file. The install.ps1 should contain:
# Define the path to the file to be copied
$fileToCopy = "<your fake app>.EXE"
# Define the destination path (Public Desktop)
$destinationPath = [Environment]::GetFolderPath("CommonDesktopDirectory")
# Build the full path of the file to be copied
$sourceFile = Join-Path -Path $PSScriptRoot -ChildPath $fileToCopy
# Build the full path of the destination file
$destinationFile = Join-Path -Path $destinationPath -ChildPath $fileToCopy
# Check if the file exists in the current directory
if (Test-Path $sourceFile -PathType Leaf) {
# Copy the file to the Public Desktop
Copy-Item -Path $sourceFile -Destination $destinationPath -Force
Write-Host "File copied successfully to Public Desktop."
} else {
Write-Host "File '$fileToCopy' not found in the current directory."
}Next, download the Win32 content prep tool and run it as admin and specify the parameters:
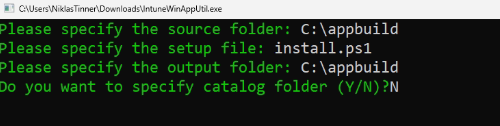
You should get an install.intunewin file — upload this to Intune as a Win32 app
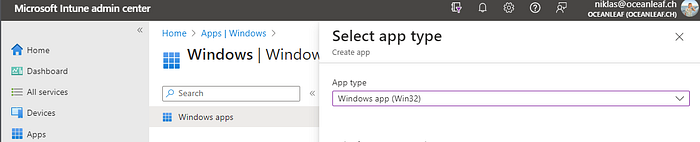
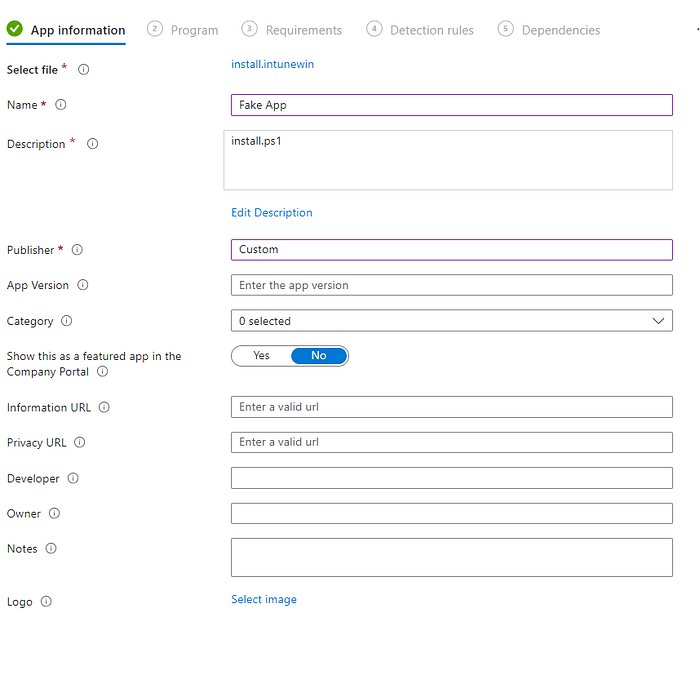
Add the following install command:
%SystemRoot%\sysnative\WindowsPowerShell\v1.0\powershell.exe -windowstyle hidden -executionpolicy bypass -command .\install.ps1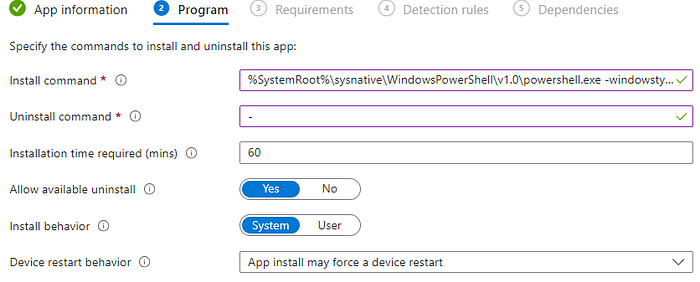
Specify requirements
Configure the detection to check for your file
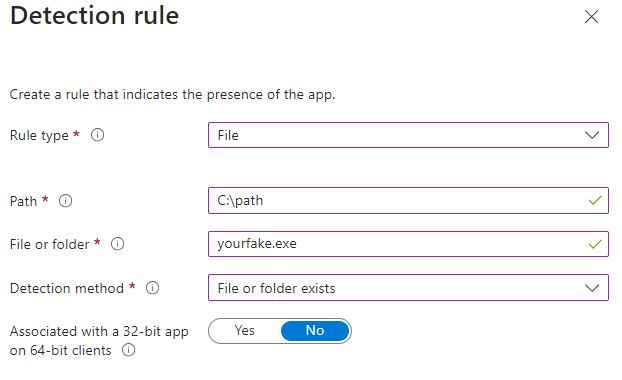
Create the app & assign.
